A recent study focusing on the state of risk-based security management (conducted by Tripwire, Inc. in collaboration with the Ponemon Institute) has found that only 46 percent of IT professionals have deployed continuous monitoring. Furthermore, many organizations that spend on perceived security risks, have not implemented preventive security technologies, and do not use audits often to identify security risks.
Let’s take a look at some of the numbers in the findings:
-
Only 50 percent of organizations said they identified specific controls at various network layers to ensure the risks were acceptable to the business and only 41 percent said they implemented layered controls to ensure a compensating control exists if one control fails.
-
93 percent of organizations have fully deployed malware detection/prevention, but only 43 percent said they have fully or partially deployed incident detection and alerts
-
Even more interesting is that only 1 percent of respondents used external audits to identify security risks and only 6 percent used internal audits. Furthermore, only 11 percent of an organization’s security budget is spent protecting the application layer, even though 37 percent of respondents identified it as a key security risk.
Some of what security professionals had to say in response to the study results:
-
Mike Fitzpatrick, NCX Group’s president and CEO, stated, “I agree with the numbers in this research data, but it is much worse in the SME space, as well as in healthcare.”
-
Dr. Larry Ponemon’s, chairman and founder of the Ponemon Institute, says, “Unfortunately, the misalignment of perceived risk and security spending coupled with the minimal use of security audits means that many organizations don’t have the information they need to improve security risks.”
-
John Pierce’s, vice president of information systems for Tripwire, voiced concern, “The risk and security landscape faced by organizations continues to increase in complexity, requiring us to deploy and manage more sophisticated and comprehensive solutions to address rapidly evolving risks.”
The study’s findings and the security professionals’ testimonials make it very clear that organizations need to drive their risk management efforts up a notch. There has to be continuous monitoring of your security system, your network must be vetted and your technologies too.
Without information security improvement how can organizations protect their data? They can’t; and this can only lead to more compromised data, loss of trust in those businesses that get breached, financial consequences due to penalties and fines for noncompliance, business costs, and so on and so forth.
Click here for the full details on the study.
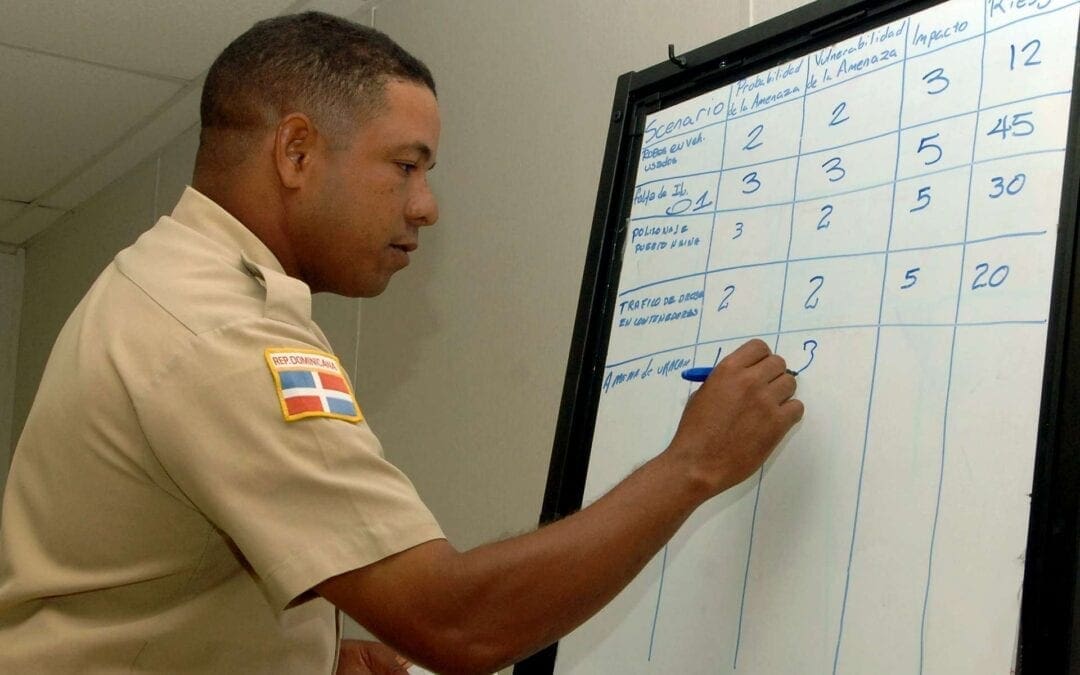
Photo courtesy of The U.S. Navy