In Marc Solomon’s Security Week Article, The Ripple Effect of Virtual Security, he talks about networks; as networks expand and evolve, so do the attack vectors and the need to ensure you do not have any gaps in your network.
In Marc Solomon’s Security Week Article, The Ripple Effect of Virtual Security, he talks about networks; as networks expand and evolve, so do the attack vectors and the need to ensure you do not have any gaps in your network.
Virtual environments have increased due to the fact that most IT groups have been asked to do more with less, due to the reduction in operating costs and flexibility to meet the changing needs of the business. This request comes at a price because IT professionals are worried about the protection of their information assets in these virtual environments.
Solomon recommends three ways to help reduce and address these concerns:
- Remove organizational silos.
IT groups have grown to a natural separation of duties with server operations owning the servers; network operations owning the routers, switches and firewalls; and security owning IT security systems, including intrusion detection and prevention systems and advanced malware protection solutions. In the virtual world it is often more difficult to involve all these groups when a new server is coming on line. Due to the often short time-frames for virtual servers it becomes the responsibility of the virtual environment team to handle all of these areas, even if they lack the experience or knowledge. IT groups should work towards creating teams which span the range of server operations, network operations, and IT security. This will help the organization identify potential gaps and ways to mitigate those risks. - Seek security solutions designed for virtual environments.
Many security solutions deployed in organizations today rely on physical appliances to protect their virtual environments. Many times this introduces unnecessary latency and management complexity. Deploying solutions specifically designed for virtual environments can ease the deployment timeframes and workflows. This does not mean those solutions are not able to protect physical assets because they should. - Target consistent security effectiveness.
When an organization implements a solution that has disparate technologies that do not work together, they also implement a solution with gaps in security protection. Your security design should take a holistic approach and view; one that provides an effective and consistent method to protect your information assets in both the physical and virtual worlds. The approach and design should allow for real-time identification and protection updates across the entire network.
NCX Group can help you evaluate and understand your current security posture for both the virtual and physical environment, and help you design a holistic approach to protecting your information assets.
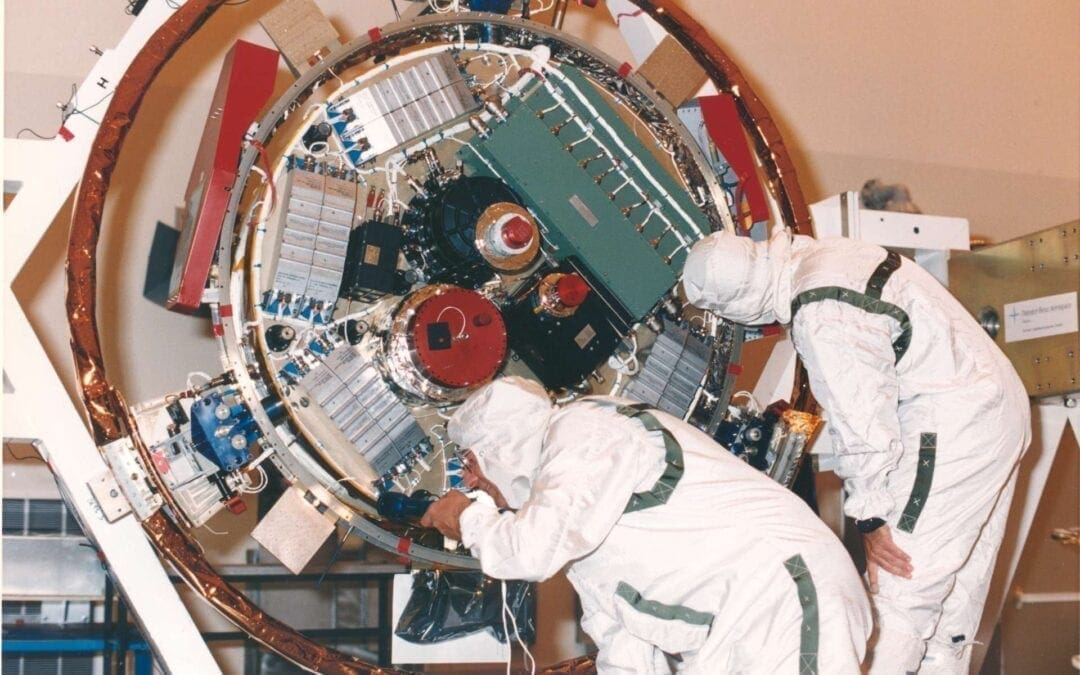
Photo Courtesy of NASA